Signals intelligence
| This article may be deleted soon. | ||
|---|---|---|
Signals intelligence, often abbreviated SIGINT is an intelligence collection discipline based on interception of signals, usually electromagnetic, between people (i.e., COMINT or communications intelligence) or between machines (i.e., ELINT or electronic intelligence), or mixtures of the two. As sensitive information is often encrypted, SIGINT often involves the use of cryptanalysis. However, traffic analysis—the study of who is signalling whom and in what quantity—can often produce valuable information, even when the messages themselves cannot be decrypted. As a means of collecting intelligence, SIGINT is a subset of intelligence collection management, which, in turn, is a subset of intelligence cycle management. Intercepting written but encrypted communications, and extracting information, probably did not wait long after the development of writing; see cipher, and a more technical discussion under cryptography. A simple encryption system, for example, is the Caesar cipher. Electronic interception appeared as early as 1900, during the Boer War. The Boers had captured some British radios, and, since the British were the only people transmitting at the time, had signals rather obvious to intercept.[1] More technical definitions of SIGINT and its branchesIn the United States of America and other nations involved with NATO, SIGINT is defined as [2]:
The JCS definition may overemphasize "foreign instrumentation signals". That part should be considered in combination with MASINT, which is closely linked to foreign instrumentation such as telemetry or radionavigation. An ELINT sensor may find a radar, and then cue (i.e., guide) a COMINT sensor for listening in on the talk between the radar and its remote users. A nonspecific SIGINT sensor can cue a Frequency Domain MASINT sensor that can help identify the purpose of the signal. If MASINT cannot identify the signal, then the intelligence organization may task an IMINT aircraft or satellite to take a picture of the source, so photointerpreters can try to understand its functions. Being a broad field, SIGINT has many sub-disciplines. The two main ones are COMmunications INTelligence (COMINT) and ELectronic INTelligence (ELINT). There are, however, some techniques that can apply to either branch, as well as to assist FISINT or MASINT. An excellent Australian analysis of how the pieces came together, from targeting to physical destruction of radars, in Operation Desert Storm was written by Carlo Kopp. There were different requirement for search radar and for the different area defense and point defense missile systems, and how these guided the Suppression of Enemy Air Defense (SEAD) attacks on the radars, command centers, and missiles. [3] TargetingA collection system has to know to look for a particular signal. "System", in this context, has several nuances. Targeting is an output of the process of developing collection requirements:
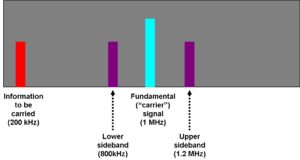
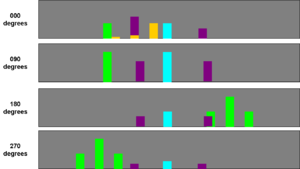
Need for multiple, coordinated receiversFirst, even with a geographically fixed target, atmospheric conditions, sunspots, the target's transmission schedule and antenna characteristics, and other factors, mean that a given signal intercept sensor is not guaranteed to be able to "hear" the signal of interest, even if the opponent made no attempt to make the signal hard to intercept. Among the most basic countermeasures against interception is frequent changing of frequency, and other transmission characteristics such as polarization. Such countermeasures mean that an intercept aircraft could not get off the ground if it had to carry antennas and receivers for every possible frequency and signal type. Second, locating the transmitter's position is usually part of SIGINT. Triangulation and more sophisticated radiolocation techniques, such as time of arrival methods, require multiple receiving points at different locations. These receivers send location-relevant information to a central point, or perhaps to a distributed system in which all participate, such that the information can be correlated and a location computed. Intercept managementModern SIGINT systems, therefore, have substantial communications among intercept platforms. Even if some platforms are clandestine, there is a broadcast of information telling them where and how to look for signals.[4] A U.S. targeting system under development in the late 1990s, PSTS, constantly sends out information that helps the interceptors properly aim their antennas and tune their receivers. Larger intercept aircraft, such as the EP-3 Aries II, RC-135 RIVET JOINT or RC-135 COMBAT SENT have the onboard capability to do some target analysis and planning, but others, such as the RC-12 GUARDRAIL, are completely under ground direction. GUARDRAIL aircraft are fairly small, and usually work in units of three to cover a tactical SIGINT requirement, where the larger aircraft tend to be assigned strategic/national missions. In other words, before the detailed process of targeting begins, someone has to decide there is a value in collecting information about something. While it would be possible to direct signals intelligence collection at a major sports event, the systems would capture a great deal of noise, news signals, and perhaps announcements in the stadium. If, however, an antiterrorist organization believed that a small group would be trying to coordinate their efforts, using short-range unlicensed radios, at the event, SIGINT targeting of radios of that type would be reasonable. Targeting would not know where in the stadium the radios might be, or the exact frequency they are using; those are the functions of subsequent steps such as signal detection and direction finding. Once the decision to target is made, the various interception points need to cooperate, since resources are limited. Knowing what interception equipment to use becomes easier when a target country buys its radars and radios from known manufacturers, or is given them as part of foreign military aid. National intelligence services keep libraries of devices manufactured by their own country and others, and then use a variety of techniques to learn what equipment is acquired by a given country. Knowledge of physics and electronic engineering further narrows the problem of what types of equipment might be in use. An intelligence aircraft flying well outside the borders of another country will listen for long-range search radars, not short-range fire control radars that would be used by a mobile air defense. Soldiers scouting the front lines of another army know that the other side will be using radios that must be portable and not have huge antennas. Signal detectionWhether a signal is human communications (e.g., a radio), the intelligence collection specialists have to know it exists. If the targeting function described above learns that a country has a radar that operates in a certain frequency range, the first step is to use a sensitive receiver, with one or more antennas that listen in every direction, to find an area where such a radar is operating. Once the radar is known to be in the area, the next step is to find its location. If operators know the probable frequencies of transmissions of interest, they may use a set of receivers, preset to the frequencies of interest. These are the frequency (horizontal axis) versus power (vertical axis) produced at the transmitter, before any filtering of signals that do not add to the information being transmitted. Received energy on a particular frequency may start a recorder, and alert a human to listen to the signals if they are intelligible (i.e., COMINT). If the frequency is not known, the operators may look for power on primary or sideband frequencies using a spectrum analyzer signals] Information from the spectrum analyzer is then used to tune receivers to signals of interest. For example, in this simplified spectrum, the actual information is at 800 KHz and 1.2 MHz. Real-world transmitters and receivers usually are directional. In the figure to the left, assume that each display is connected to a spectrum analyzer connected to a directional antenna aimed in the indicated direction. Countermeasures to interceptionSpread-spectrum communications is an electronic counter-countermeasures (ECCM) technique to defeat looking for particular frequencies. Spectrum analysis can be used in a different ECCM way, to identify frequencies not being jammed or not in use. Direction-findingThe earliest, and still common, means of direction finding is to use directional antennas as goniometers, so that a line can be drawn from the receiver through the position of the signal of interest. HF/DF, pronounced "huff-duff", was the term used in the Battle of the Atlantic in locating German submarines. Knowing the compass bearing, from a single point, to the transmitter does not locate it. Where the bearings from multiple points, using goniometry, are plotted on a map, the transmitter will be located at the point where the bearings intersect. This is the simplest case; a target may try to confuse listeners by having multiple transmitters, giving the same signal from different locations, switching on and off in a pattern known to their user but apparently random to the listener. Since modern weapons can home in on and attack transmitters, the antennas of a military unit frequently are placed a hopefully safe distance from the user of the transmitter. While this is much more difficult for ships, moving ground vehicles, and aircraft, even they may do so by towing antennas or putting the transmitter in an unmanned aerial vehicle. Individual directional antennas have to be manually or automatically turned to find the signal direction, which may be too slow when the signal is of short duration. One alternative, now obsolete, is to use the Wullenweber array technique. In this method, several concentric rings of antenna elements simultaneously receive the signal, so that the best bearing will ideally be clearly on a single antenna or a small set. Wullenweber arrays for high-frequency signals are enormous, referred to as "elephant cages" by their users. The current alternative to tunable directional antennas, or large omnidirectional arrays such as the Wullenweber, is to measure the time of arrival of the signal at multiple points, the points using GPS or a similar method to have precise time synchronization. The points at which the receivers can be placed can be on ground stations, ships, aircraft, or satellites, giving great flexibility. Traffic analysisWhen locations are known, usage patterns may emerge, and inferences drawn. Traffic analysis is the discipline of drawing patterns from information flow among a set of senders and receivers, whether those senders and receivers are designated by location determined through direction finding, by addressee and sender identifications in the message, or even MASINT techniques for "fingerprinting" transmitters or operators. Message content, other than the sender and receiver, is not necessary to do traffic analysis, although more information can be helpful. For example, if a certain type of radio is known to be used only by tank units, even if the position is not precisely determined by direction finding, it may be assumed that a tank unit is in the general area of the signal. Of course, the owner of the transmitter can assume someone is listening, so might set up tank radios in an area where he wants the other side to believe he has actual tanks. As part of Operation Quicksilver, part of the deception plan for the invasion of Europe at the Battle of Normandy, radio transmissions simulated the headquarters and subordinate units of the fictitious First United States Army Group (FUSAG), commanded by George Patton, to make the German defense think that the main invasion was to come at another location. In like manner, fake radio transmissions from Japanese aircraft carriers, before the attack on Pearl Harbor, were made from Japanese local waters, while the attacking ships moved under strict radio silence. Traffic analysis need not focus on human communications. For example, if the sequence of a radar signal, followed by an exchange of targeting data and a confirmation, followed by observation of artillery fire, this may identify an automated counterbattery system. A radio signal that triggers navigational beacons could be a landing aid system for an airstrip or helicopter pad that is intended to be low-profile. Patterns do emerge. Knowing a radio signal, with certain characteristics, originating from a fixed headquarters may be strongly suggestive that a particular unit will soon move out of its regular base. The contents of the message need not be known to infer the movement. There is an art as well as science of traffic analysis. Expert analysts develop a sense for what is real and what is deceptive.[5]. Modern hobbyist, monitoring radio communications, can have quite sophisticated approaches. [6] Electronic Order of BattleGenerating an Electronic order of battle (EOB) requires identifying SIGINT emitters in an area of interest, determining their geographic location or range of mobility, characterizing their signals, and, where possible, determining their role in the broader organizational order of battle. EOB covers both COMINT and ELINT. [7] The Defense Intelligence Agency maintains an EOB by location. The Joint Spectrum Center (JSC) of the Defense Information Systems Agency supplements this location database with five more technical databases:
For example, several voice transmitters might be identified as the command net (i.e., top commander and direct reports) in a tank battalion or tank-heavy task force. Another set of transmitters might identify the logistic net for that same unit. An inventory of ELINT sources might identify the medium- and long-range counter-artillery radars in a given area.[8] If a commander knows he is facing such sensors, he will try to attack a different area with his artillery. SIGINT units will identify changes in the EOB, which might indicate enemy unit movement, changes in command relationships, and increases or decreases in capability. Using the COMINT gathering method enables the intelligence officer to produce an electronic order of battle by traffic analysis and content analysis among several enemy units. For example, if the following messages were intercepted:
This sequence shows that there are two units in the battlefield, unit 1 is mobile, while unit 2 is in a higher hierarchical level, perhaps a command post. One can also understand that unit 1 moved from one point to another which are distant from each 20 minutes with a vehicle. If these are regular reports over a period of time, they might reveal a patrol pattern. Direction-finding and Radiofrequency MASINT could help confirm that the traffic is not deception. The EOB buildup process is divided as following:
Separation of the intercepted spectrum and the signals intercepted from each sensors must take place in an extremely small period of time, in order to separate the deferent signals to different transmitters in the battlefield. The complexity of the separation process depends on the complexity of the transmission methods (e.g., hopping or time division multiple access (TDMA)). By gathering and clustering data from each sensor, the measurements of the direction of signals can be optimized and get much more accurate then the basic measurements of a standard direction finding sensor.[9] By calculating larger samples of the sensor's output data in near real-time, together with historical information of signals, better results are achieved. Data fusion correlates data samples from different frequencies from the same sensor, "same" being confirmed by direction finding or radiofrequency MASINT. If an emitter is mobile, direction finding, other than discovering a repetitive pattern of movement, is of limited value in determining if a sensor is unique. MASINT then becomes more informative, as individual transmitters and antennas may have unique sidelobes, unintentional radiation, pulse timing, etc. Network build-up among between each emitter (communication transmitter) to another enables creation of the communications flows of a battlefield[10]. FISINTForeign instrumentation signals intelligence (FISINT) is a sub-category of ELINT, monitoring primarily non-human communication. Foreign instrumentation signals include (but not limited to) telemetry (TELINT), tracking systems, and video data links. TELINT is an important part of national means of technical verification for arms control. SIGINT versus MASINT
SIGINT and Measurement and Signature Intelligence (MASINT) are closely, and sometimes confusingly, related [11]. The SIGINT disciplines of communications and electronic intelligence focus on the information in those signals themselves, as with COMINT detecting the speech in a voice communication or ELINT measuring the frequency, pulse repetition rate, and other characteristics of a radar. MASINT also works with collected signals, but is more of an analysis discipline. There are, however, unique MASINT sensors, typically working in different regions or domains of the electromagnetic spectrum, such as infrared or magnetic fields. While NSA and other agencies of the United States intelligence community have MASINT groups, the Central MASINT Office is in the Defense Intelligence Agency (DIA). Where COMINT and ELINT focus on the intentionally transmitted part of the signal, MASINT focuses on unintentionally transmitted information. For example, a given radar antenna will have sidelobes emanating from other than the direction in which the main antenna is aimed. The RADINT (radar intelligence) discipline involves learning to recognize a radar both by its primary signal, captured by ELINT, and its sidelobes, perhaps captured by the main ELINT sensor, or, more likely, a sensor aimed at the sides of the radio antenna. MASINT associated with COMINT might involve the detection of common background sounds expected with human voice communications. For example, if a given radio signal comes from a radio used in a tank, if the interceptor does not hear engine noise or higher voice frequency than the voice modulation usually uses, even thought the voice conversation is meaningful, MASINT might suggest it is a deception, not coming from a real tank. Defensive SIGINTThere are a number of ways that a person or organization can defend against SIGINT. There is a delicate balance between the level of protection and the actual threat, as expressed in the clichés about "tinfoil hats". One must begin by defining the threat. It is considerably more difficult to defend against detection that one is signaling, as opposed to defending against an opponent discovering the content of the transmitted message. Appropriate encryption can protect against content interception, but protecting against signal detection, especially with a capable opponent, requires measures to make the signal hard to detect -- which can also make it difficult for the intended recipient to receive the signal. Any defensive program needs to consider the nature of the threat and the capabilities of the opponent. Strong and well-managed encryptionWhile encryption is discussed at length in other articles, it should not be forgotten that if one wants to protect messages and files, encryption is central to the defense. As important as the encryption process itself may be, it is vulnerable if the cryptographic keys are not strong and protected, and, on computers, that the cleartext is deleted when not needed. Seemingly obvious, but too often neglected, is making a practice of having as little cleartext hard copy as possible. Appropriate transmission securityWhen using radio transmitters, use directional antennas that have as little "spillover" into sidelobes as possible. If it is most important to hide the location of a transmitter, the minimum is to cable the antennas as far as possible away from the transmitter proper. In many circumstances, aiming the antenna upward to a satellite will help hide its location. The amount of total transmission power needs to be minimized, and the power preferably should be split into multiple and changing frequencies using spread spectrum techniques. If possible, avoid transmitting when hostile SIGINT satellites or monitoring aircraft are overhead. If in an urban area, avoid using regular commercial power to transmit. There are ways in which the signal can "leak" into power and ground lines. The adversary may turn off power to an area, which will tell him there is a line-operated transmitter if the transmission stops, and that there is a battery-powered transmitter if it continues. Use highly variable transmission schedules and vary frequencies if technically possible. Also see low probability of intercept. Appropriate receiving securityIf Operation RAFTER-style intercept is a threat, protect against this form of unintentional radiation MASINT by using optoisolators or other shielded techniques (e.g, waveguides) to bring in the radio frequency received signal, and shield the local oscillator and intermediate frequency stages in the superheterodyne receiver. This technique should be far less effective against the new generation of software-defined radio. Unintentional radiation on power or ground circuits is a threat here as well; use appropriate TEMPEST or other techniques. Protection against compromising emanationsThere are risks that electronic, acoustic, or other information could "leak" from a computer system or other electronic communications devices. The RiskUnderstanding details of the risks requires a substantial knowledge of electronics, but a simple example might serve. Many people have put a radio receiver near a computer, to listen to music as they work, and discovered that the radio suffered clicks, squeals, and other interference. These interfering signals are radiating from various parts of the computer, especially its display but often also from the power and grounding system. TEMPEST is the name for one family of protective measures against an opponent intercepting these emanations and extracting sensitive information from them. While not strictly within the scope of protecting against "leakage", a place where sensitive information is processed or discussed needs protection against hidden microphones, wiretaps, and other "bugging". Sometimes, an electronic sweep to verify TEMPEST compliance reveals the presence of hidden transmitters. Again, there is probably more suspicion than reality in most cases. A member of a crime organization, in the middle of a nasty divorce, or a foreign intelligence agent might have reason to worry, but, even with the serious questions about warrantless surveillance in the US and other countries, there is little reason for someone to go to the risk and expense of illegal surveillance on an ordinary citizen. TEMPEST is usually associated with direct electromagnetic radiation from the device, either free-space or through power and ground lines. TEMPEST generically talks about acoustic isolation, but that is fairly easily solved through physical security and noise damping, as well as searches for microphones. There are several threats that have not been officially defined in the unclassified literature. Nevertheless, there are some informed guesses [12]:
Mitigation and CountermeasuresThe word TEMPEST itself, and its meaning, are unclassified. Some of the techniques for measuring the compliance of a piece of equipment, or whether it is actually emitting compromising emanations, are classified. A good deal of the information has come into public view either through Freedom of Information Act queries[13], books talking about interception techniques, inferences drawn from partially released documents, and straightforward thinking by electronic engineers. Some documents released fully or partially under FOIA: A number of individuals have made a hobby of ferreting out TEMPEST and related information[17], and firms in the broader-than-TEMPEST business of Technical Surveillance Countermeasures TSCM also reveal concepts[18]. Protection against side channel attacks and covert channelsA side channel attack is an unintentional vulnerability of an encryption device, not related to the encryption algorithm.[19] Potential vulnerabilities include different processing and thus transmission speeds for blocks of plaintext with certain statistical characteristics, changes in power consumption, or compromising emanations. Covert channels are deliberate means to elude communications security[20]. They send out an unauthorized signal by stealing bandwidth from a legitimate, often encrypted channel. One low-bandwidth method would be to send information by varying the inter-block transmission times. A steganographic covert channel might use the low-order bit of pixels in a graphic image, perhaps not even consecutive pixels, in a manner that would not be obvious to a person looking at the graphic. People of SIGINTPeople who work in SIGINT often work under heavy stress. First, it is a secret world, about which they cannot share their work with outsiders, and must conform to intense security scrutiny. Second, the work can take immense patience and concentration. An informal mental health check on cryptanalysts is to show them a telephone directory: if they start looking for patterns, and scream in frustration, they need rest if not treatment. Security aspects have led to tragedies, such as that of Alan Turing,[21] although most Western signals intelligence agencies now accept open homosexuality. There is always the danger, however, that the oppressive security will not detect a serious spy. Mental health concerns are very real. William Friedman, arguably the greatest cryptanalyst in history, broke down in 1940, before the final breach of the Japanese PURPLE system, and never could return to full-time cryptanalysis.  Memorial, inside the National Security Agency headquarters building, to all personnel who died on SIGINT duty SIGINT collectors can and do die in action; the first American killed in the Vietnam War, SP4 James T. Davis was a soldier on a SIGINT mission.[22] References
|
||
- Articles for deletion April
- CZ Live
- Military Workgroup
- Computers Workgroup
- Security Subgroup
- Intelligence Subgroup
- Signals intelligence Subgroup
- Articles written in American English
- Advanced Articles written in American English
- All Content
- Military Content
- Computers Content
- Military tag
- Security tag
- Intelligence tag
- Signals intelligence tag